A Contemporary Overview of Smart Card Support on macOS
Why Smart Card?
MIT uses certificates to authenticate users. Personally I regard this method as superior to traditional password-based authentication, but sometimes I need to log in on a new machine and it is neither convenient nor secure to install certificate on every machine that I may use. Fortunately, I have a Yubikey on my keyring which happens to provide PIV Smart Card functionality. So I spent some time figuring out how to install a certificate on it and use that to log in to MIT websites on macOS.
How “Contemporary”?
PIV Smart Card support on macOS has changed a lot (for the better) in the past several years, and many tutorials/documentations on the internet are no longer relevant, even the ones maintained by Yubico. Previously I had a post on how to install MIT certificate on Yubikey, so I decided to update that post and add some up-to-date information.
This post is organized into two parts. The first part describes how to install a certificate on Yubikey, and the second part discusses about the support of Smart Card on latest macOS releases.
The first part describes how to install (import) a certificate on Yubikey, taking the MIT certificate as an example.
Obtain the Certificate
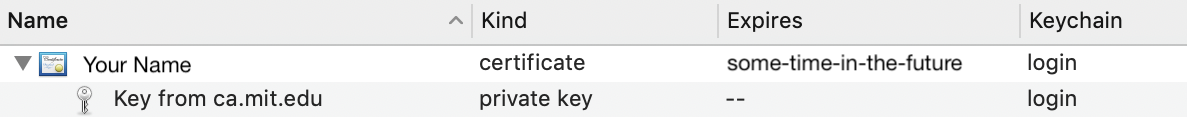
Head over to the IST website and generate a certificate. Then import it into Mac’s Keychain. You now should have the certificate and the corresponding private key listed in the Keychain Access app, like this:
Then, select the entry and hit ⇧⌘E (Shift-Command-E) to export the item. Choose “Personal Info Exchange (.p12)” format. Keychain will then ask for a passphrase to protect the file, which will be used to encrypt the exported private key. This passphrase will be needed only once, when importing the private key into Yubikey.
Import into Yubikey
Use Homebrew to install the Yubico PIV Tools by executing brew install yubico-piv-tool. Then plug in your Yubikey and import the certificate and the private key
yubico-piv-tool -s 9a -i Certificates.p12 -a import-key -a import-cert -K PKCS12
yubico-piv-tool -a set-ccc
yubico-piv-tool -a set-chuidThe first command moves the certificate (and the private key) to slot 9a on the Yubikey. Slot 9a is for authenticating the user. The second and the third commands reset some kind of UID of the Yubikey so that macOS will recognize it as a new PIV Smart Card.
The second part describes the support for Smart Cards on macOS.
Before Sierra
Before Sierra (10.12), macOS had little support for Smart Cards. Actually this statement is not totally true - up until Lion (10.7), macOS had native support for Smart Cards through tokend, a low level service that reads Smart Cards and populates the user’s Keychain. However in Lion, Apple started deprecating tokend and offloaded it from the OS installation to an open source project. Nevertheless, the underlying APIs used by tokend still exist. Users who need to work with Smart Cards can get an open source implementation of tokend by installing OpenSC.
Sierra
Fast-forward to Sierra. Apple took a change and restarted supporting PIV-compliant Smart Cards natively using a new set of APIs (CryptoTokenKit). Also natively supported is using Smart Cards for authentication. Users can associate a Smart Card (specifically, the certificate installed on the card) to the account and use the Smart Card and the PIN to login.
On Sierra, when a Smart Card is inserted, a new keychain is automatically populated. This keychain is visible in both command line and the Keychain Access application, consisting of the certificates installed on the card. Those certificates are automatically accessible to applications through the keychain API automatically.
High Sierra
In High Sierra (10.13), a new keychain is no longer created when the card is plugged in. Instead, the certificates installed on the Smart Card populates the user keychain and automatically accessible by Mail and Safari. But there is a catch - those certificates are invisible in the Keychain Access app, nor can they be retrieved by the security command line tool. Many tutorials written in the Sierra era were not updated to mention this change, causing me much confusion when I inserted the Smart Card and saw nothing being added to the keychain. Fortunately there are alternatives to check whether the certificates are recognized by the system, the simplest way being the command system_profiler SPSmartCardsDataType. This command shows all information about the Smart Card and will list the certificates when there are any. Or, just go ahead and try using the private keys in Mail or Safari, by signing an email or authenticating on a website.
Conclusion
On High Sierra and later releases, users do not need to install any third-party software to use PIV Smart Cards. Just notice that the certificates on the cards will not appear at usual locations like Keychain Access app and security find-identity. Certificates on Smart Cards works with Safari and Mail, but I’ve yet to test on other applications, such as Firefox, Chrome, and code signing.